MXDR for Google Cloud
What can Wannacry and Petya outbreaks teach us about cybersecurity?
What can Wannacry and Petya outbreaks teach us about cybersecurity?
1:55
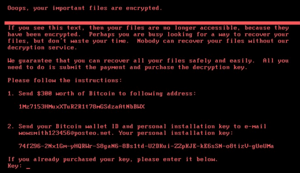
Organizations worldwide have been affected by the Wannacry and Petya ransomware strains.
What can these latest attacks teach us about cybersecurity?
- Cybersecurity must be proactive – If you aren’t proactively preparing for threats like Wannacry and Petya and taking steps to prevent them, you will be impacted by them. The costs of being reactive and having to investigate, remediate, and then put the protections and in place that you could have implemented to protect yourself will be high – and hopefully you won’t have to factor in costs for notification and credit monitoring of affected parties, or litigation and lost business due to reputational damage.
- Cybersecurity needs to be ongoing – It’s not enough to scan occasionally and pen test annually. A true cybersecurity program is ongoing, and includes regular (at least monthly) vulnerability scanning, staff awareness training, testing of both technical and human controls, monitoring and threat intelligence to detect unusual behavior, and incident response planning and resources.
- Multiple layers of defenses need to be in place – Don’t rely solely on technical controls, don’t assume your cybersecurity process and policies are being followed perfectly at all times, don’t fail to have a plan and experts to call on should an incident occur, and consult with a commercial insurer that specializes in cyber insurance to make sure you have appropriate coverage for all aspects of the cost of an incident should you need it.
A member of the Foresite cybersecurity team noted that these ransomware attacks are essentially a global vulnerability scan. It’s frightening to see how many organizations are continuing to fail the test, but yours doesn’t have to be one of them.
Click here for details of Adobe and Microsoft patches for the flaws that Wannacry and Petya ransomware stains exploit.